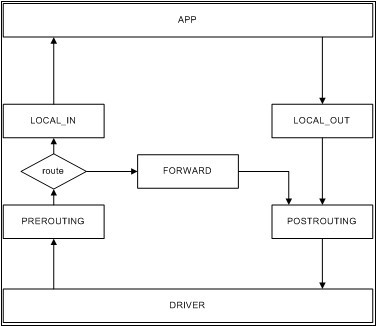
Linux netfilter提供了五個hook的注冊點,分別為NF_INET_PRE_ROUTING、NF_INET_LOCAL_IN、NF_INET_FORWARD、NF_INET_LOCAL_OUT、NF_INET_POST_ROUTING。這五個hook點在Linux協議棧中調用之處如下:
NF_INET_PRE_ROUTING --> ip_rcv():
點擊(此處)折疊或打開
return NF_HOOK(NFPROTO_IPV4, NF_INET_PRE_ROUTING, skb, dev, NULL,
ip_rcv_finish)
NF_INET_LOCAL_IN? -->??ip_local_deliver():
點擊(此處)折疊或打開
return NF_HOOK(NFPROTO_IPV4, NF_INET_LOCAL_IN, skb, skb->dev, NULL,
ip_local_deliver_finish)
NF_INET_FORWARD --> ip_forward():
點擊(此處)折疊或打開
return NF_HOOK(NFPROTO_IPV4, NF_INET_FORWARD, skb, skb->dev,
rt->dst.dev, ip_forward_finish);
NF_INET_LOCAL_OUT?--> __ip_local_out():
點擊(此處)折疊或打開
return nf_hook(NFPROTO_IPV4, NF_INET_LOCAL_OUT, skb, NULL,
skb_dst(skb)->dev, dst_output);
NF_INET_POST_ROUTING?--> ip_output():
點擊(此處)折疊或打開
return NF_HOOK_COND(NFPROTO_IPV4, NF_INET_POST_ROUTING, skb, NULL, dev,
ip_finish_output,
!(IPCB(skb)->flags & IPSKB_REROUTED));
內核中典型的鉤子有:
點擊(此處)折疊或打開
一、nf_nat_ipv4_ops
static struct nf_hook_ops nf_nat_ipv4_ops[] __read_mostly = {
/* Before packet filtering, change destination */
{
.hook????????= nf_nat_ipv4_in,
.owner????????= THIS_MODULE,
.pf????????= NFPROTO_IPV4,
.hooknum????= NF_INET_PRE_ROUTING,
.priority????= NF_IP_PRI_NAT_DST,
},
/* After packet filtering, change source */
{
.hook????????= nf_nat_ipv4_out,
.owner????????= THIS_MODULE,
.pf????????= NFPROTO_IPV4,
.hooknum????= NF_INET_POST_ROUTING,
.priority????= NF_IP_PRI_NAT_SRC,
},
/* Before packet filtering, change destination */
{
.hook????????= nf_nat_ipv4_local_fn,
.owner????????= THIS_MODULE,
.pf????????= NFPROTO_IPV4,
.hooknum????= NF_INET_LOCAL_OUT,
.priority????= NF_IP_PRI_NAT_DST,
},
/* After packet filtering, change source */
{
.hook????????= nf_nat_ipv4_fn,
.owner????????= THIS_MODULE,
.pf????????= NFPROTO_IPV4,
.hooknum????= NF_INET_LOCAL_IN,
.priority????= NF_IP_PRI_NAT_SRC,
},
};
二、ipv4_synproxy_ops
static struct nf_hook_ops ipv4_synproxy_ops[] __read_mostly = {
{
.hook????????= ipv4_synproxy_hook,
.owner????????= THIS_MODULE,
.pf????????= NFPROTO_IPV4,
.hooknum????= NF_INET_LOCAL_IN,
.priority????= NF_IP_PRI_CONNTRACK_CONFIRM - 1,
},
{
.hook????????= ipv4_synproxy_hook,
.owner????????= THIS_MODULE,
.pf????????= NFPROTO_IPV4,
.hooknum????= NF_INET_POST_ROUTING,
.priority????= NF_IP_PRI_CONNTRACK_CONFIRM - 1,
},
};
三、ip_vs_ops
static struct nf_hook_ops ip_vs_ops[] __read_mostly = {
/* After packet filtering, change source only for VS/NAT */
{
.hook????????= ip_vs_reply4,
.owner????????= THIS_MODULE,
.pf????????= NFPROTO_IPV4,
.hooknum????= NF_INET_LOCAL_IN,
.priority????= NF_IP_PRI_NAT_SRC - 2,
},
/* After packet filtering, forward packet through VS/DR, VS/TUN,
* or VS/NAT(change destination), so that filtering rules can be
* applied to IPVS. */
{
.hook????????= ip_vs_remote_request4,
.owner????????= THIS_MODULE,
.pf????????= NFPROTO_IPV4,
.hooknum????= NF_INET_LOCAL_IN,
.priority????= NF_IP_PRI_NAT_SRC - 1,
},
/* Before ip_vs_in, change source only for VS/NAT */
{
.hook????????= ip_vs_local_reply4,
.owner????????= THIS_MODULE,
.pf????????= NFPROTO_IPV4,
.hooknum????= NF_INET_LOCAL_OUT,
.priority????= NF_IP_PRI_NAT_DST + 1,
},
/* After mangle, schedule and forward local requests */
{
.hook????????= ip_vs_local_request4,
.owner????????= THIS_MODULE,
.pf????????= NFPROTO_IPV4,
.hooknum????= NF_INET_LOCAL_OUT,
.priority????= NF_IP_PRI_NAT_DST + 2,
},
/* After packet filtering (but before ip_vs_out_icmp), catch icmp
* destined for 0.0.0.0/0, which is for incoming IPVS connections */
{
.hook????????= ip_vs_forward_icmp,
.owner????????= THIS_MODULE,
.pf????????= NFPROTO_IPV4,
.hooknum????= NF_INET_FORWARD,
.priority????= 99,
},
/* After packet filtering, change source only for VS/NAT */
{
.hook????????= ip_vs_reply4,
.owner????????= THIS_MODULE,
.pf????????= NFPROTO_IPV4,
.hooknum????= NF_INET_FORWARD,
.priority????= 100,
},
#ifdef CONFIG_IP_VS_IPV6
/* After mangle & nat fetch 2:nd fragment and following */
{
.hook????????= ip_vs_preroute_frag6,
.owner????????= THIS_MODULE,
.pf????????= NFPROTO_IPV6,
.hooknum????= NF_INET_PRE_ROUTING,
.priority????= NF_IP6_PRI_NAT_DST + 1,
},
/* After packet filtering, change source only for VS/NAT */
{
.hook????????= ip_vs_reply6,
.owner????????= THIS_MODULE,
.pf????????= NFPROTO_IPV6,
.hooknum????= NF_INET_LOCAL_IN,
.priority????= NF_IP6_PRI_NAT_SRC - 2,
},
/* After packet filtering, forward packet through VS/DR, VS/TUN,
* or VS/NAT(change destination), so that filtering rules can be
* applied to IPVS. */
{
.hook????????= ip_vs_remote_request6,
.owner????????= THIS_MODULE,
.pf????????= NFPROTO_IPV6,
.hooknum????= NF_INET_LOCAL_IN,
.priority????= NF_IP6_PRI_NAT_SRC - 1,
},
/* Before ip_vs_in, change source only for VS/NAT */
{
.hook????????= ip_vs_local_reply6,
.owner????????= THIS_MODULE,
.pf????????= NFPROTO_IPV4,
.hooknum????= NF_INET_LOCAL_OUT,
.priority????= NF_IP6_PRI_NAT_DST + 1,
},
/* After mangle, schedule and forward local requests */
{
.hook????????= ip_vs_local_request6,
.owner????????= THIS_MODULE,
.pf????????= NFPROTO_IPV6,
.hooknum????= NF_INET_LOCAL_OUT,
.priority????= NF_IP6_PRI_NAT_DST + 2,
},
/* After packet filtering (but before ip_vs_out_icmp), catch icmp
* destined for 0.0.0.0/0, which is for incoming IPVS connections */
{
.hook????????= ip_vs_forward_icmp_v6,
.owner????????= THIS_MODULE,
.pf????????= NFPROTO_IPV6,
.hooknum????= NF_INET_FORWARD,
.priority????= 99,
},
/* After packet filtering, change source only for VS/NAT */
{
.hook????????= ip_vs_reply6,
.owner????????= THIS_MODULE,
.pf????????= NFPROTO_IPV6,
.hooknum????= NF_INET_FORWARD,
.priority????= 100,
},
#endif
};
四、ipv4_conntrack_ops
static struct nf_hook_ops ipv4_conntrack_ops[] __read_mostly = {
{
.hook????????= ipv4_conntrack_in,
.owner????????= THIS_MODULE,
.pf????????= NFPROTO_IPV4,
.hooknum????= NF_INET_PRE_ROUTING,
.priority????= NF_IP_PRI_CONNTRACK,
},
{
.hook????????= ipv4_conntrack_local,
.owner????????= THIS_MODULE,
.pf????????= NFPROTO_IPV4,
.hooknum????= NF_INET_LOCAL_OUT,
.priority????= NF_IP_PRI_CONNTRACK,
},
{
.hook????????= ipv4_helper,
.owner????????= THIS_MODULE,
.pf????????= NFPROTO_IPV4,
.hooknum????= NF_INET_POST_ROUTING,
.priority????= NF_IP_PRI_CONNTRACK_HELPER,
},
{
.hook????????= ipv4_confirm,
.owner????????= THIS_MODULE,
.pf????????= NFPROTO_IPV4,
.hooknum????= NF_INET_POST_ROUTING,
.priority????= NF_IP_PRI_CONNTRACK_CONFIRM,
},
{
.hook????????= ipv4_helper,
.owner????????= THIS_MODULE,
.pf????????= NFPROTO_IPV4,
.hooknum????= NF_INET_LOCAL_IN,
.priority????= NF_IP_PRI_CONNTRACK_HELPER,
},
{
.hook????????= ipv4_confirm,
.owner????????= THIS_MODULE,
.pf????????= NFPROTO_IPV4,
.hooknum????= NF_INET_LOCAL_IN,
.priority????= NF_IP_PRI_CONNTRACK_CONFIRM,
},
};
五、ipv4_defrag_ops
static struct nf_hook_ops ipv4_defrag_ops[] = {
{
.hook????????= ipv4_conntrack_defrag,
.owner????????= THIS_MODULE,
.pf????????= NFPROTO_IPV4,
.hooknum????= NF_INET_PRE_ROUTING,
.priority????= NF_IP_PRI_CONNTRACK_DEFRAG,
},
{
.hook = ipv4_conntrack_defrag,
.owner = THIS_MODULE,
.pf = NFPROTO_IPV4,
.hooknum = NF_INET_LOCAL_OUT,
.priority = NF_IP_PRI_CONNTRACK_DEFRAG,
},
};
enum nf_ip_hook_priorities {
NF_IP_PRI_FIRST = INT_MIN,
NF_IP_PRI_CONNTRACK_DEFRAG = -400,
NF_IP_PRI_RAW = -300,
NF_IP_PRI_SELINUX_FIRST = -225,
NF_IP_PRI_CONNTRACK = -200,
NF_IP_PRI_MANGLE = -150,
NF_IP_PRI_NAT_DST = -100,
NF_IP_PRI_FILTER = 0,
NF_IP_PRI_SECURITY = 50,
NF_IP_PRI_NAT_SRC = 100,
NF_IP_PRI_SELINUX_LAST = 225,
NF_IP_PRI_CONNTRACK_HELPER = 300,
NF_IP_PRI_CONNTRACK_CONFIRM = INT_MAX,
NF_IP_PRI_LAST = INT_MAX,
};
NF_INET_PRE_ROUTING鏈:
ipv4_conntrack_in(-200)? ipv4_conntrack_defrag(-400) ip_vs_preroute_frag6(-99) nf_nat_ipv4_in(100)
NF_INET_LOCAL_IN鏈:
ip_vs_reply4(98) ip_vs_remote_request4(99) ip_vs_reply6(98)ip_vs_remote_request6(99) ipv4_helper(300) nf_nat_ipv4_fn(100) ipv4_synproxy_hook(INT_MAX-1) ipv4_confirm(INT_MAX)
NF_INET_FORWARD鏈:
ip_vs_forward_icmp(99)? ip_vs_forward_icmp_v6(99)?ip_vs_reply4(100) ip_vs_reply6(100)
NF_INET_LOCAL_OUT鏈:
ipv4_conntrack_defrag(-400)?ipv4_conntrack_local(-200)?nf_nat_ipv4_local_fn(-100) ip_vs_local_reply4(-99)?ip_vs_local_reply6(-99)ip_vs_local_request4(-98) ip_vs_local_request6(-98)
NF_INET_POST_ROUTING鏈:
nf_nat_ipv4_out(100) ?ipv4_helper(300)ipv4_synproxy_hook(INT_MAX-1) ipv4_confirm(INT_MAX)
netfilter框架
版权声明:本站所有资料均为网友推荐收集整理而来,仅供学习和研究交流使用。

工作时间:8:00-18:00
客服电话
电子邮件
admin@qq.com
扫码二维码
获取最新动态